Just published a new updated and completely refactored version of the sp_CloneRights stored procedure.
The new version is available in my SQL Scripts repository on GitHub under the RightsManagement folder.
Procedure internals were completely refactored, added a new option in the to script classes (MS_SHIPPED). With this new script class the procedure now by default does not script permissions for schema bound objects which have set property “is_ms_shipped” – this means an object marked as system object. If you want to script permissions for such objects, you need to specify the MS_SHIPPED explicitly in the script classes list.
New parameters and parameters enhancements
The @scriptClass parameter was further enhanced and now supports wildcards. Example below shows scripting of permissions on all schema-scope objects except CLR objects.
sp_CloneRights
@principal = '%'
,@scriptClass = 'OBJECT,-%CLR%'
Previous versions added printing of informational messages about the permissions being assigned. current version further improves those information, but also introduces @noInfoMsgs parameter, which when set to 0 does not outputs that into the final script. How ti behaves can be seen in samples below in the New Output format section.
Azure Support
Stored procedure now supports also Azure SQL Database. When deploying procedure to azure SQL Database, remove or comment-out the unsupported USE [master] statement. You can also remove the USE statement in case you can to create the procedure in the user database. By default on SQL Server instance the procedure is created in the master database and marked as system object. Thanks to this it can be executed easily in every database and in case not specifying the @database parameter it runs in the context of current database.
/* *****************************************************************************************
AZURE SQL DB Notice
Comment-out the unsupported USE [master] when running in Azure SQL DB/Synapse Analytics
or ignore error caused by unsupported USE statement
***************************************************************************************** */
USE [master]
GO
New Output format
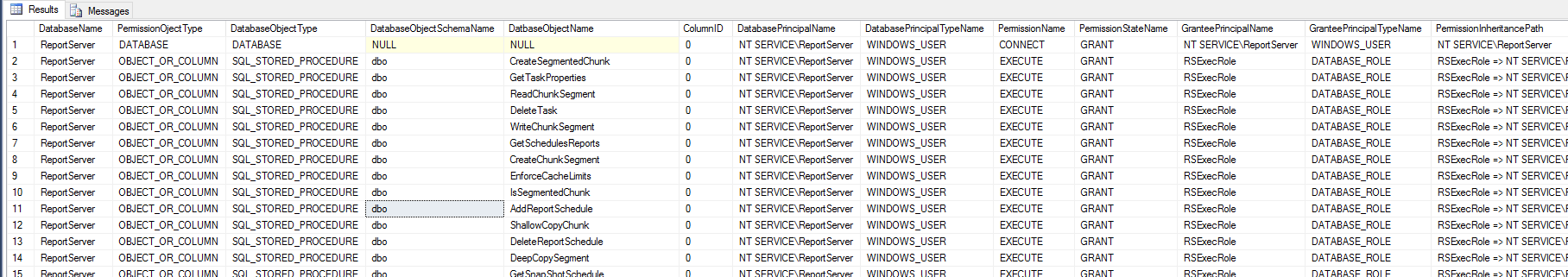
Output of the function was changed so the script is no longer printed in to messages window of SSMS, but instead the procedure returns the script as a result set, which can be easily copied to target target window.

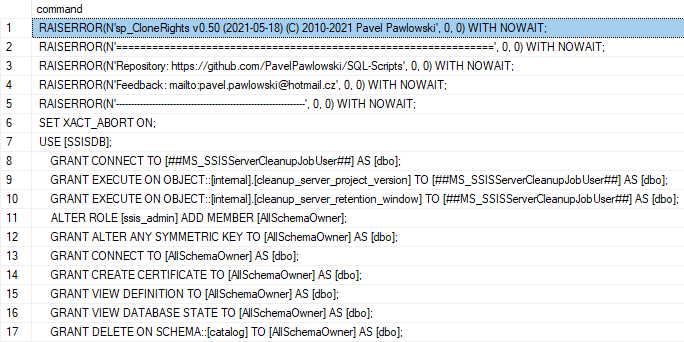
It is possible to use @noInfoMsg = 1 parameter to remove the printing of the informational messages from the script and keep only the permissions related statements:
Help for the updated function is available in the GitHub Wiki.
This article is follow-up of the previous related posts SQL Server – Cloning User Rights – updated sp_CloneRights on GitHub and Cloning user rights in database.